Buying & Importing Cars · Car Care & Maintenance · The African Autos
Total Car Cost When Importing Secondhand
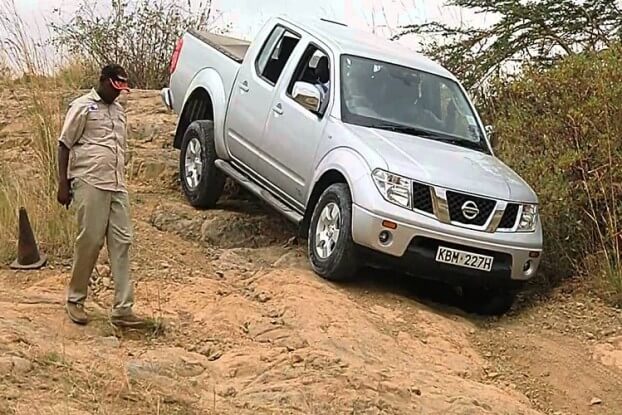
The jargon… you want to import a used car from Japan. You visit the BEFORWARD site and see some very nice cars. Let’s say you are from Kenya. Now, the government has put forth very strict measures about the age of the car that you can import second-hand. The oldest[...]